Static vs Dynamic Malware Analysis | A Brief Comparison
Malware analysis or malicious code analysis helps to get us a superior comprehension of how to deal with any malicious threats. To recognize and analyze malware, there are two sorts of techniques used by experts; one is static malware analysis and the other is dynamic malware analysis.
In this article, we will be discussing the differences between these two malware analysis techniques, so that you can understand both processes while comparing them to each other.
Therefore, let’s get into them without wasting time!
What is Static Malware Analysis?
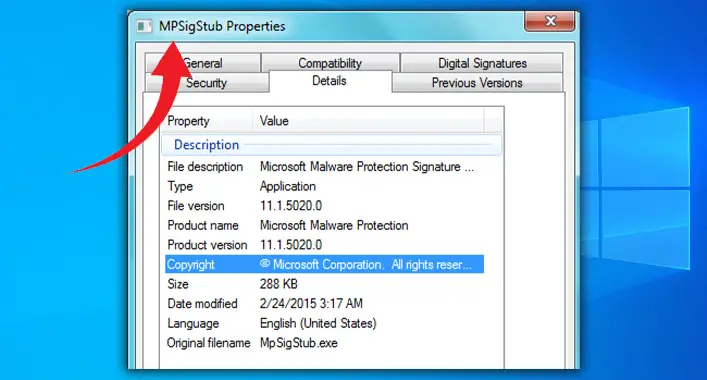
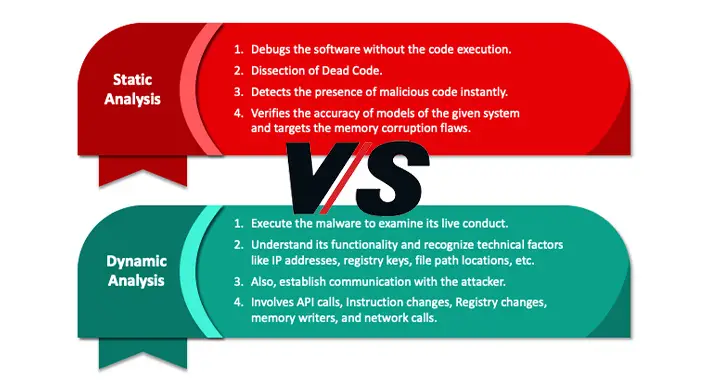
Through static analysis, the malware binary is analyzed without running the malicious code. It is performed by determining the signature of a malicious binary file. As you know, the signature of a binary file is the unique identification of it and this can be done by calculating the cryptographic hash of the file. This helps the analyzer to understand the characteristics of each component.
To reverse-engineer the malware binary file, the executable is loaded into the dissembler like IDA. The executable can convert the code into a language code, that helps the analyst to read and understand the code easily. Also, this allows the expert to have a perfect understanding of the capabilities of malware binary code.
What is Dynamic Malware Analysis?
This malware analysis process requires running the malware sample on a system to analyze and observe the behavior and characterization of the sample. It helps the debugger to know about the infection type and the ways to stop the infection. The analyst uses a virtual machine to study thoroughly the malware characterization, behavior, risks, and stopping the process.
What are the Differences Between Static and Dynamic Malware Analysis?
The core difference between the Static and Dynamic Malware Analyzation process remains in the understanding process of these processes. Even though both analysis processes are equally appreciated, the differences make it more convenient to choose the one that is suitable for you. A comparison of the core differences between these two analyzing processes is given below –
| Static Malware Analysis | Dynamic Malware Analysis |
| Analyzing malicious binary codes without actually running the code on any system is called Static Malware Analysis Process. | Analyzation and monitoring process of a malicious program that requires to be executed in a virtual environment. |
| The signature-based approach is used in this process to analyze the malicious binary. | The behavior-based approach is used in this process to analyze and detect malicious programs. |
| File fingerprinting, virus scanning, binary reverse-engineering, file obfuscations, analyzing the memory artifacts, packer detection, and debugging are part of Static Malware Analysis. | API calls, instruction traces, registry changes, network, and system calls, and memory writing access are some parts of Dynamic Malware Analysis. |
This analysis process is only effective against some sophisticated malware programs and codes. | This analysis process is effective for every type of malicious program and code, including the most sophisticated malware programs. |
| The static Malware Analysis process does not require to be run the malicious binary on a computer system. | Dynamic Malware Analysis process required to run the malicious binary on a computer system. |
Frequently Asked Questions (FAQs)
What Is Malware Analysis Tool?
While analyzing the behavior of malware, you need to use some programs, applications, or programs. Malware analysis tools are the programs or applications that are used in the malware analysis process.
Can Malware Analysis Reduce False Positives?
No, it cannot reduce false positives. But it can lead the security tools to make detection errors, increasing false-positive rates. As you know, false positives are the main drawback of the malware detection process.
What Are the Three 3 Phases of Malware Analysis?
Behavioral, code, and memory forensics are the three phases of the malware analysis process. These phases help the expert understand the examined malware’s pros and cons.
Finishing Lines
As you have known, detection, identification, and preliminary analysis are important for malware analysis. Both static and dynamic malware analysis process is widely used techniques to analyze malicious binary, codes, or programs. The static malware analysis technique is a signature-based analysis process, whilst the dynamic analysis process is based on behavior. That’s all for today, have a great day.
![[Explained] Can A Virtual Machine Get A Virus?](https://cyberselves.org/wp-content/uploads/2022/10/Can-A-Virtual-Machine-Get-A-Virus.jpg)

![[Answered] Can a 3DS Get a Virus?](https://cyberselves.org/wp-content/uploads/2023/09/Can-a-3DS-Get-a-Virus.webp)
![Can You Get a Virus from Opening a Snapchat? [Explained]](https://cyberselves.org/wp-content/uploads/2023/03/Can-You-Get-a-Virus-from-Opening-a-Snapchat.webp)