What Are the Examples of Worm Malware? A Complete Guide
Have you ever heard of worm malware? Well, it can replicate itself automatically to spread on multiple device systems. To do so, the computer worm doesn’t need a helping hand not even from malicious actors. Keep reading this article to know more about the worm malware, its spreading process, and examples. So, let’s start;

What Is a Worm and How Does It Work?
As you already know, how much damage can worm cause to the human body. Like that, the computer worms are an insidious type of malicious program that is designed to spread across multiple device systems and remain active on each device system. Worms with a payload can open the backdoor for the hackers to take the control of the systems.
However, computer worms are significantly dangerous to a computer system, because of their capability. After getting into a device system, it is able to spread throughout the entire network and computing system without any external action from the malicious actor. Being so, worms do not need to con the user to get into a device system. By exploiting hidden vulnerabilities on the OS; worms can get into a device system.
Worm relied on the physical mean of a device system to get into the entry point of a network. External means like floppy discs, USB drives, and other media drives are used by the malicious actor for injecting worms into a device system. After that, the malicious actor waits for the unassuming victim or user to insert the malicious drive into the device system. Despite being an old technique; it is still viable. Even today, a good deal of corporate espionage and sabotage are conducted by using this seemingly-innocuous worm injecting process.
In recent times, hackers and cybercriminals are using electronic means to spread the worms on device systems. Email, instant messaging services, and file-sharing networks are some electronic means used by malicious actors to spread worms.
What Are the Examples of Worms Malware?
There are mainly two types of worm malware; one that uses physical means to spread through the devices and the other that uses electronic means to spread. Email worms, file sharing worms, instant messaging worms, and internet worms are some examples of worms that use electronic means to spread. USB flash drives, floppy discs, and other physical means are used by other types of worms. Here are detailed examples of some infamous worm malware;
1. The Morris Worm Malware
Created by Robert Tappan Morris on 2nd November 1998 was one of the pre-historic computer worms. Though it wasn’t created to cause actual damage, due to the writing method, it was able to infect its host machines multiple times. For creating this worm malware, Morris became the first person to be convicted under the US Computer Fraud and Abuse Act 1986.
2. ILOVEYOU
Earlier in this millennium (the early 2000’s), ILOVEYOU worm malware emerged in the Philippines before spreading throughout the world. It was spread through the mail message named ILOVEYOU, and it was designed to overwrite files of the victim device system randomly.
3. SQL Slammer
SQL (Structured Query Language) slammer was a brute-force internet worm that infected roughly 75,000 device systems in only 10 minutes in the early 2003’s. Using the email tactics, it was spread by targeting the vulnerability that existed on Microsoft’s SQL Server for Windows 2000. It randomly generated IP addresses at random and spreads copies of itself to these IP addresses.
4. WannaCry
This is one of the most recent examples of how devastating worm malware could be. It was a kind of ransomware that encrypted the files of the infected device system and demanded ransom to return access to the files. Even with modern cybersecurity systems, it had infected, 2,30,000 PCs in 150 countries in 2017’s.
Is a Worm a Virus?
Is worm a virus? No, the worms and the virus are not the same things. The main difference between a computer worm and a virus remains in the spreading techniques. As mentioned, a worm can spread the copies of itself to other machines completely on its own, while the virus is not able to do that without help from the hacker or cyber attacker. Though, both of them is a kind of malicious codes that can cause significant damage to a device system. So, despite being malicious for a device, the worm is not a kind of virus.
Frequently Asked Questions (FAQs)
What Is the Difference between Virus and Worm?
The main difference between a computer worm and a virus remains in the spreading techniques. As mentioned, a worm can spread the copies of itself to other machines completely on its own, while the virus is not able to do that without help from the hacker or cyber attacker.
Is Trojan Virus a Worm?
The Trojan cannot replicate itself like viruses and worms. Instead, it hides in the system as a piece of the system to steal important and confidential information from the user.
Are Worms Removable?
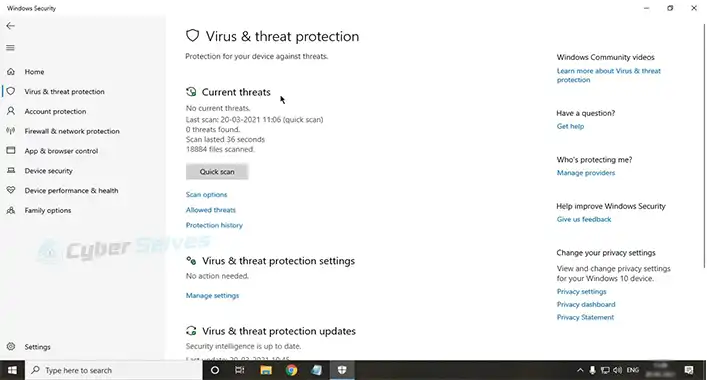
Yes, some malware and virus removal tools can remove worm malware from a device system. Moreover, they also prevent the worms from coming back multiple times. Microsoft’s Malicious Software Removal Tool is one of the tools that can remove worms from a device system.
Conclusion
As you have known about the worm malware, its examples, and the working process; beware of it. Else it could cause damage to the device system. The expert suggests using trusted sources to transfer files and messaging for avoiding worm malware attacks. That’s all for today, have a great day.
![[ANSWERED] Can a Motherboard Get a Virus?](https://cyberselves.org/wp-content/uploads/2023/09/Can-a-Motherboard-Get-a-Virus.webp)
![Can You Get a Virus from Opening a Snapchat? [Explained]](https://cyberselves.org/wp-content/uploads/2023/03/Can-You-Get-a-Virus-from-Opening-a-Snapchat.webp)