How to Safely Test Malware? Malicious Code Testing
Analyzing malicious codes is not an easy task for a basic computer user. There are some complications and risks while testing a malicious code sample. Is it possible to safely test malware? The answer is ‘Yes’. Still, you have to be careful. In this article, we will be discussing the methods of safely analyzing a malicious sample.
What are the Phases of ‘Safely Testing Malware’?
It is better to divide any task into different phases, which helps to complete the task easily and properly. There is three-phase of analyzing the process for malware, Behavioral analysis, Code analysis, and Memory analysis. A brief outline of each phase is given below;
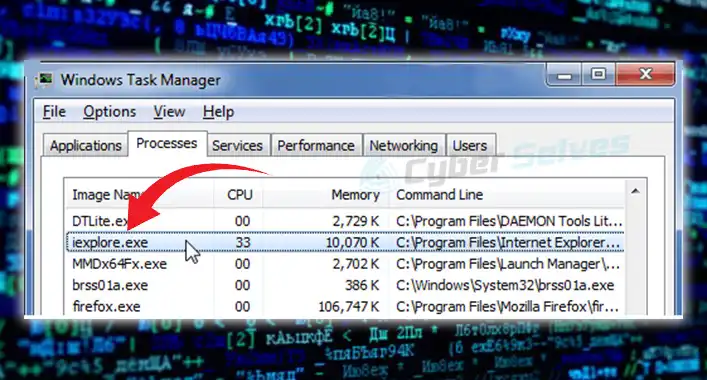
Behavioral Analysis
In this phase, you have to examine the malware sample’s interaction with different locations of the device system and OS components. Some free tools like Process Monitor, Process Explorer, RegShot, and Wireshark can help you to do so.
Code Analysis
This is the second phase of analyzing a malware sample. In this phase, IT experts reverse-engineer the malicious sample to understand the code that defines the behavior of the malware. To analyze the malicious codes, you can use OllyDbg and IDA Pro.
Memory Analysis
Analyzing the memory is the third and final phase of analyzing a malicious sample. This phase will help to identify malicious codes like rootkits. Moreover, this process can clarify the program’s run-time dependencies and can explain how the specimen was used on the victim’s system. The volatility framework plugins can be used to analyze the memory.
How to Safely Test Malware?
To safely analyze a malware sample, you can use different sources. These sources will automatically test the malware samples for you. Here is a brief outline of testing malware samples from different sources;
1. Using Free Source
Some free sources can help you to analyze malicious codes and files. It is always better to use these sources in addition to downloading and analyzing samples from known malicious URLs. Here are some of the sources that can help you to analyze malicious codes or file samples;
– ANY.RUN
– MalShare
– VirusBay
– Yomi
2. Using Virtual Machine (VM)
Virtual machines are computer file that behaves like an actual computer device without any physical structure. You can use it to analyze the malware samples manually. Here are the steps that you should follow to analyze malware samples through a virtual machine;
Step-1 Create a virtual machine and choose the Operating System. Afterward, allocate RAM with a minimum of 1 GB.
Step-2 Create a virtual hard disk as similar as possible to the physical hard disk. It will allow the malware to access files, folders, and programs of the VM (Virtual machine).
Step-3 Allocate storage by a fixed value.
Step-4 Thereafter, install the guest OS and then get the VM running.
Step-5 Snapshot the VM (Similar to the restore point of Windows).
Frequently Asked Questions (FAQs)
What Is Malware Sample?
Malware samples are provided to the engineer or IT experts to reverse engineer them. Through the malware sample, malicious codes are analyzed. And the analysis process helps to prevent that specific malware infection.
Are Virtual Machines Safe?
Despite being great alternatives to physical computers, virtual machines are still vulnerable to malicious attacks. Also, a virtual machine has guest-to-guest and guest-to-host security issues, which don’t exist in physical machines.
Can You Install Software on a Virtual Machine?
Yes, you can install software on a virtual machine. It works like an online computer without any physical structures. So, you can use a virtual machine as a physical device.
Conclusion
At this point, you have known enough about safe malware testing. If you are manually analyzing a malware sample; use a virtual machine. To automatically analyze the malware samples, you need to use online sources for safety. That’s all for today, have a great day.
![[ANSWERED] Can You Have Avast and Malwarebytes Simultaneously?](https://cyberselves.org/wp-content/uploads/2023/08/Can-You-Have-Avast-and-Malwarebytes-Simultaneously.webp)
![Is Bandicam a Virus? [Answered]](https://cyberselves.org/wp-content/uploads/2023/03/Is-Bandicam-a-Virus.webp)
![Can You Get a Virus from a Zip File? [Explained]](https://cyberselves.org/wp-content/uploads/2022/11/Can-You-Get-a-Virus-from-a-Zip-File.jpg)