What Is Tailgating in Cyber Security?
In recent days, social engineering threats are emerging. Tailgating is a kind of social engineering attack that may cause huge damage to your organization. This attack is conducted to disclose the private or sensitive information of an organization. But, what is tailgating attack? Why does this type of attack conduct for? Keep reading this article to know more about tailgating attacks.

What Is Tailgating in Cyber Security?
Tailgating is a type of social engineering attack that enables hackers or attackers to get access to a password-protected location. It involves closely following an authorized individual to get the access credentials of a restricted or personal location. According to some cyber security experts, tailgating is an unconscious act of a similar scenario happening without consent. A successful tailgating attack allows the attackers to get into the restricted location of the device and network system of an organization. Tailgating attempts to do not work in all systems or environments of a company. Especially, the organizations that use entry-oriented security protocols in place.
Some organizations are pretty much vulnerable to a tailgating attack. Organizations that use multiple entrance points on the network system locations are most vulnerable to tailgating attacks. Also, organizations with numerous employees are vulnerable to tailgating attacks. Though, the multifactor authentication process will reduce the risk of tailgating attacks.
What are the Common Examples of Tailgating?
The actors of tailgating attacks include outsiders who have no relation with the organizations and disgruntled ex-employees looking to avenge the perceived injustices. Here are some examples that will clarify how tailgating attacks can happen;
– The classic example of tailgating attack is when the outsider gets the password or login credentials of the organization from the insider employees. The password or login credentials allow others to get into the system.
– Other examples of tailgating attacks when an ex-employee looking for avenging the perceived injustice. Which is pretty much possible.
What to do to Prevent Tailgating Attacks?
It is not impossible to prevent tailgating attacks you need to follow some steps to protect your organization against tailgating attacks. Here are the measures you should follow to avoid tailgating attacks;
1. Train Employees in Physical Security
Some organization focuses their security awareness training program to educate them on digital security practices that include proper password and login credential hygiene and recognizing phishing and spamming. This will reduce the risks of tailgating attacks.
2. Familiarize Employees with Social Engineering
Many employees don’t recognize the tailgating attacks because of their unfamiliarity with the social engineering attacks. Making them familiar with the symptoms and detection methods of social engineering attacks will ensure the protection of you and your organization against the social engineering attacks including tailgating attacks.
3. Improving Physical and Cyber Access Security
Improving the physical and cyber access security of your organization will make your organization more secure against illegal access. Moreover, it will enhance the security and privacy of your organization.
4. Use Advanced Video Surveillance
Advanced video surveillance is necessary to monitor the access point (physical) of the organization. It will allow you to monitor the physical entrance of your organization. So, using advanced video surveillance will make your device against tailgating attacks.
5. Multi-Factor Authentication Process
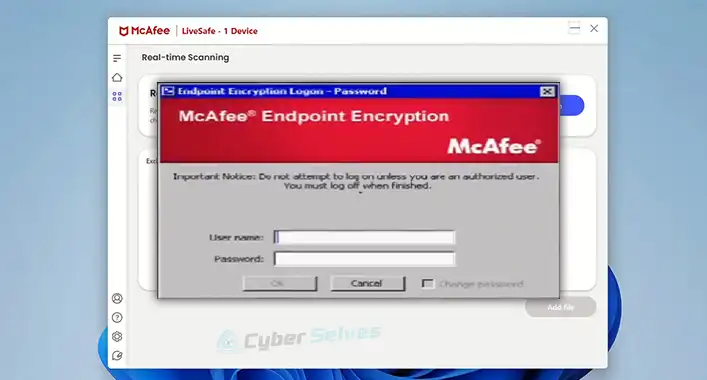
The multifactor authentication process is necessary to secure the access point of your organization. You can apply biometrics authentication for physical entrances and multifactor authentication processes to keep you protected against tailgating attacks.
Frequently Asked Questions (FAQs)
Are Tailgating and Security Breaching the Same?
Tailgating is a kind of physical security breach in which an unauthorized person follows an authorized individual to enter secured premises. That means tailgating is a type of security breach.
What Is the Difference between Piggybacking and Tailgating?
The main difference between piggybacking and tailgating is tailgating implies no consent while piggybacking implies the consent of the authorized person. Though, some security experts describe tailgating and piggybacking as the same thing.
What are Social Engineering Threats?
Social engineering threats are the malicious activities accomplished through human interactions. These types of threats use psychological manipulation to conduct damage.
Final Words
At this point, you have known enough about the tailgating attacks and their impact on your organization. This type of attack may cause huge damage to your organization and implementing the multi-factor authentication process is the most effective solution to prevent tailgating attacks. That’s all for today, have a great day.