Which Process Is Used to Protect Transmitted Data in a VPN?
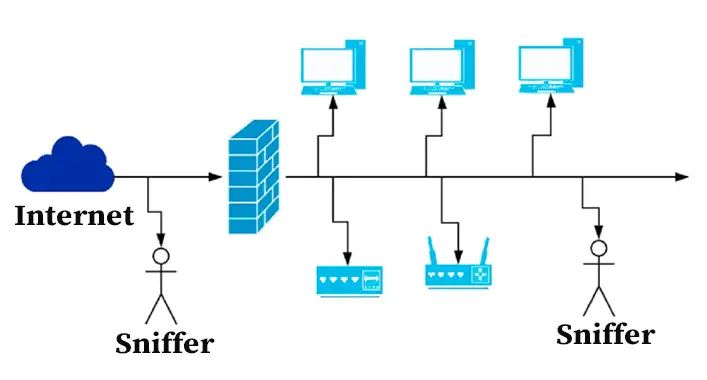
Encrypting data before sending it over the network is a typical procedure. This ensures that only the designated receiver can decode and read the data. Another common procedure is to create a safe tunnel between the two devices. This tunnel prohibits outsiders from monitoring and reading the data as it is transferred.
Data encryption is the process of encoding data so that only authorized parties can read it. When it comes to data transmission, it’s critical to select a method that keeps the data secure as it travels from one point to another.
VPNs are widely used to transmit sensitive data between sites. The following article discusses some most prevalent types of data encryption procedures used in VPNs and how they are implemented.
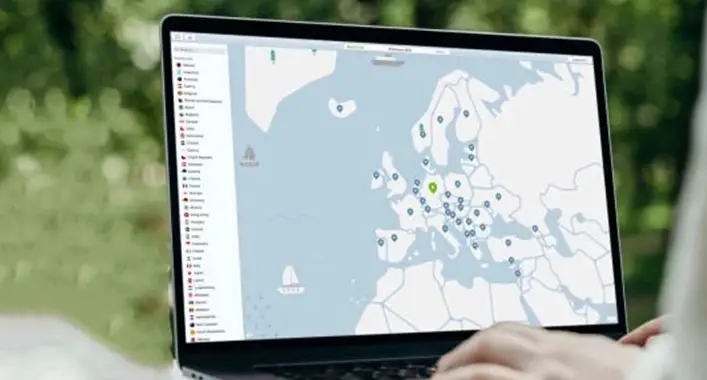
Understanding What VPN Is
A VPN (virtual private network) is a way to improve your security and privacy by encrypting data sent to your Internet service provider. It also aids in the protection of sensitive information from hackers, snoopers, and government surveillance.
To accomplish this, it secures both the user’s computer or device and all data flowing between them. This ensures that only authorized computers may decrypt and read sent data, even if intercepted en route.
VPN Data Encryption Processes
Data encryption is the process of converting data into code that cannot be easily read. Data encryption assures the safety and security of electronic information, both while it is delivered over the internet and when it is kept on devices or servers.
A VPN, or Virtual Private Network, protects personal information by encrypting any digital data sent from point A to point B. There are numerous methods for encrypting data, each with its own level of security.
Understanding What Tunneling Is
Tunneling is the process of sending users’ data through an encryption protocol (or tunnel) so that third parties cannot access it. Tunneling makes it easier to send data across public networks, such as the internet, because all of your information is encrypted before it leaves your computer and then re-encrypted once it arrives at its destination. It is frequently used when communicating sensitive information such as financial or medical records over an insecure network such as the internet.
Which Process Is Used to Protect Transmitted Data in a VPN – Various Data Encryption Processes Used in VPNs
In this section, you can find a variety of different data encryption processes that are utilized in VPNs.
Private Tunneling Protocol
VPNs do not encrypt data, but instead rely on two other features: tunneling and protocol. Tunneling procedures are classified into two types: one-layer (or double-layer) and multi-layer. One-layer tunneling conceals the user’s identity by encrypting each packet, but multiple-layer tunneling encrypts the identity as well as the payload data.
Ip Protection (Ipsec)
One of the most used methods for protecting transferred data is IPSec. IPSec is a reasonable and very effective approach to keep sensitive information such as trade secrets or health care records private and safe when traveling over the Internet.
The Authentication Header (AH) and the Encapsulating Security Payload (ESP) are two components of an IPSec protocol suite (ESP). These two protocols collaborate to provide security services for data in transit.
OpenVPN
OpenVPN Community Edition (also known as OpenVPN CE) is a Virtual Private Network (VPN) project that uses open-source software. It establishes secure connections over the Internet by utilizing a unique security protocol that employs SSL/TLS. Many OpenVPN Inc. employees support this community-supported OSS (Open Source Software) project, which uses a GPL license.
Secure Socket Tunneling Protocol (SSTP)
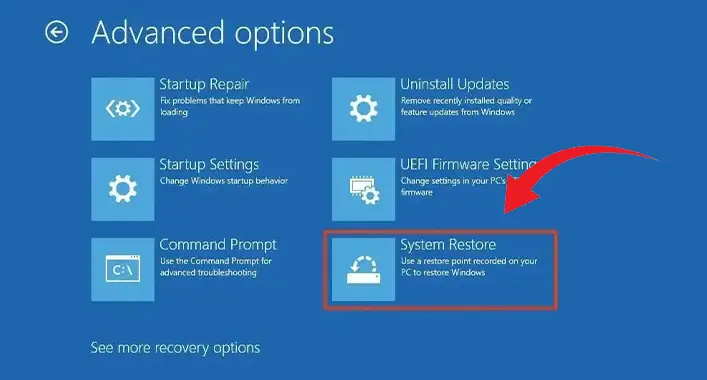
One example is the Secure Socket Tunneling Protocol (SSTP). This protocol, which is available on Windows and macOS, can create a secure connection by routing the internet connection through TCP port 443.
Layer 2 Tunneling Protocol With Internet Protocol Security (l2tp/Ipsec)
L2TP/IPsec is a VPN tunneling protocol that supports data encryption. L2TP uses the more secure IPsec protocol for encryption. It can be used to establish point-to-point connections, such as from a remote user’s computer to a company’s private network via the Internet. It lacks server support and has limited utility.
Secure Shell (SSH)
Secure Shell (SSH) is a cryptographic network protocol to establish secure encrypted connections between two computers. This process is typically carried out over a network such as an internet, but it can also be carried out using point-to-point tunneling technologies. SSH, unlike the SSL and TLS protocols, does not require authentication before connecting.
Advantages
- VPN encryption protects private data in transit between two points.
- Using a VPN to encrypt your data keeps your communications, connection, and data information safe from prying eyes.
- When it comes to security, it doesn’t take much these days for any data you send over the internet to be intercepted.
- Many people are wary of using public WiFi because they believe hackers can steal their personal information via unsecured connections.
- Communication is increasingly moving online.
Disadvantages
There are numerous disadvantages to using a VPN. For starters, a VPN may not be able to prevent government data mining. Some users may experience increased website blocking as a result of this change. This can limit the user’s surfing abilities as well as their access to services, information, and files.
Data encryption can consume a lot of energy, potentially leading to an increase in global energy consumption. Geo-blocking and the inability of businesses outside China, Iran, and Syria to use VPN services if their country’s laws or government restrict it are further issues.
Last Words
The process used to protect transmitted data is determined by the provider and protocol you use, as well as the level of encryption desired. The type of process used determines how complicated the setup is, so consider your skill level before making a decision. If you only want to protect your personal internet usage and don’t need a lot of bells and whistles, tunneling may be a better option.