What Is Eldorado Virus and What Does It Do? Everything You Need to Know
In this digital age, I’ve faced the formidable challenge posed by the Eldorado Virus. As someone who’s navigated the ever-evolving realm of online security, I’ve encountered this issue firsthand.
So, what exactly is the Eldorado Virus, and what impact does it have? It presented me with problems that demanded my attention, and I realized that solutions are essential. I delved into these difficulties and explored the methods to protect my digital space.
Fortunately, I discovered ways to shield myself from this digital menace. In the upcoming sections, I’ll guide you through the methods and steps to counter the challenges presented by the Eldorado Virus. I firmly believe that knowledge is our best defense, and by the end of this article, you’ll be well-equipped to safeguard your digital realm against this looming threat.
The world of the Eldorado Virus is complex and ever-evolving, and I’ve come to understand that a deeper comprehension is vital. Read on to unravel its mysteries, comprehend its impact, and learn how to fortify your defenses effectively. Your journey to digital security begins here.

Eldorado Virus: What Does It Defind?
One day, our gadgets run seamlessly, and the next, confronted with a new challenge. Among these challenges, one that has gathered quite a bit of attention is the Eldorado Virus. Let’s discuss the whole thing about the Eldorado.
The Eldorado virus is a malicious software program designed by cybercriminals with nefarious intentions. It’s important to note that this virus is not an everyday computer virus; it’s far more insidious. This is not your run-of-the-mill hiccup; it’s a malicious presence that can wreak havoc on your digital life.
Knowing where the Eldorado Virus came from helps us understand its dangers. This malware’s been around a while, changing to stay effective against our defenses.
How Does Eldorado Virus Operate?
To discover the workings of this digital threat. Explore its invasion, data theft, and remote-control tactics, important for safeguarding your digital world.
1. The Invasion Process
Picture this: your computer is like a fortress, and the Eldorado virus is a cunning infiltrator. It primarily enters your system through deceptive email attachments, infected downloads, or malicious websites. Once it’s in, the virus starts a covert takeover, lurking in the shadows of your digital world.
2. Data Theft
The main purpose of the Eldorado virus is to steal your data. It’s like a digital burglar, quietly working in the background to compromise your personal information, such as financial data, login credentials, and even sensitive documents.
3. Remote Control and Manipulation
One of the most concerning aspects of this virus is its ability to grant remote access to cybercriminals. They can manipulate your computer, potentially causing a wide array of issues, from identity theft to unauthorized access to your online accounts.
To protect yourself effectively, understand the Eldorado Virus’s operation. In the next part, we’ll discuss the impact of the Eldorado Virus.
The Impact of the Eldorado Virus
Learn about what happens when the Eldorado Virus strikes. From losing your data to letting hackers control your system, find out how it can affect your online safety.
1. Financial Consequences
The consequences of falling victim to the Eldorado virus can be dire. Imagine dealing with unauthorized financial transactions, drained bank accounts, and credit card fraud. This is not a scenario anyone would want to experience.
2. Privacy Violations
Your privacy is at stake when dealing with Eldorado. The virus can capture personal information, including your browsing history, chat logs, and even your webcam activity. This invasion of your private life is a grave concern.
3. System Instability
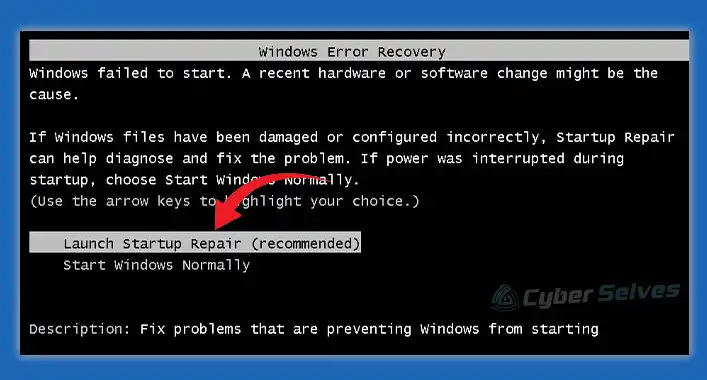
The Eldorado virus can also make your computer sluggish and prone to crashes. This creates frustration and inconvenience, making your daily digital activities feel like a never-ending quandary.
Protecting Yourself Against Eldorado Virus
Secure your digital world with tips for keeping yourself safe against the Eldorado Virus. Learn how to shield your data, keep intruders out, and ensure your online safety.
1. Stay Informed
The first step in safeguarding your digital life is to stay informed. Keep up with the latest cybersecurity news and trends to better understand the evolving landscape of digital threats.
2. Use Antivirus Software
Invest in reliable antivirus software to create an added layer of protection. Regularly update it to ensure you’re well-prepared to fend off threats like Eldorado.
3. Practice Safe Browsing Habits
Avoid opening suspicious emails or downloading files from untrustworthy sources. Exercise caution when clicking on links and regularly update your passwords.
Frequently Asked Questions (FAQs)
Is the Eldorado virus the same as a regular computer virus?
No, the Eldorado Virus is not the same as a regular computer virus. It’s a distinct type of malware with specific characteristics and behaviors.
What are the primary infection vectors of the Eldorado Virus?
The Eldorado Virus employs multiple infection methods, including malicious email attachments, deceptive websites, and exploiting software vulnerabilities. Understanding these vectors is crucial for protection.
Can the Eldorado Virus be removed without professional help?
Removing the Eldorado Virus is a complex task that often requires professional assistance. Attempting to remove it independently can lead to further damage or data loss.
How can I protect my computer from the Eldorado Virus?
You can protect your computer by using reputable antivirus software, keeping your operating system and software up to date, and practicing safe browsing habits to avoid malicious downloads.
What are the warning signs of an Eldorado Virus infection?
Warning signs include slow system performance, unauthorized file changes, and ransom demands for data decryption. Recognizing these signs is vital for swift action.
Does paying the ransom guarantee data recovery after an Eldorado Virus attack?
Paying a ransom is risky and not guaranteed to result in data recovery. It’s better to explore other options, such as data recovery services or consulting with experts.
Can businesses be specifically targeted by the Eldorado Virus?
Yes, businesses are often targeted due to the potential for larger financial gains. They must take extra precautions to safeguard their data.
Are there any free tools for Eldorado Virus removal and decryption?
While some free tools may be available, it’s essential to exercise caution. Consult with cybersecurity experts for guidance on using reliable solutions.
How can I back up my data to protect against the Eldorado Virus?
To protect against data loss, regularly back up your files to an external device or cloud storage. Ensure your backups are isolated from the network to prevent infection.
Is it possible to trace the origin of the Eldorado Virus attacks?
Tracing the origin of these attacks can be challenging as cybercriminals often use various methods to hide their identities. It typically requires extensive investigations by cybersecurity experts.