Which is the Most Secure Type of Firewall? The necessity of Secured Firewalls
Every device or system needs something to prevent or avoid its threats of it. That’s where the necessity of security programs and devices begins. These security programs may come in software or hardware version. A firewall is a kind of security tool that monitors the traffic of the network and protects a device from various threats. There are many types of firewalls available, but which type should you pick to ensure maximum protection?

What is a Firewall?
A firewall is a kind of security device that protects a network system by filtering traffic and blocking unauthorized access. Also, it helps a user to keep away malicious software or program (virus, malware, Trojans, worms, ransomware, spyware) from infecting a computer or device. The firewall of a computer device or network acts as a gatekeeper, monitors access to the operating system to avoid unwanted and unrecognized traffic.
How Does Firewall Works?
Every firewall has some rule to analyze the network traffic. It only accepts the connections that are configured to accept by the configured rules. To do so, it allows or blocks specific data packets or communication units through the digital network because the firewall applies the pre-configured security rules.
On the gateway or port of a computer or device, it acts as a traffic guard to allow only the trusted sources or IP addresses on the system. It rejects unauthorized and unanimous traffic on the primary stage. Also, it scans the incoming data packets which are for potential security threats. If the firewall detects any data packet as a threat, it prevents the data packets from reaching the network or computing device.
Which is the Most Secure Type of Firewall? – Showing Types of a Firewall
There are five basic types of firewalls that are used to protect data and devices from destructive cyber elements and other potential threats. The five types of the firewall and their characteristics are given below;
1. Packet-Filtering/ Stateless Firewall
The packet-filtering or stateless firewalls is one of the entry-level firewalls and sometimes, these types of firewalls may run into difficulties while differentiating the legitimate and undesired connections. This is called a packet-filtering firewall because it only checks the data packets and ignores the network traffic and connections of a computer system. A stateless firewall lets the packet pass or block by comparing the data criteria which include IP address, port number, any types of data packets. This type of firewall offers a low level of security, lower resource consumption, and higher performance speeds on a device or system.
Packet-filtering techniques are not able to keep away all types of attacks and threats from a network or computing system. This cannot defend a system against spoofing and other attacks that are conducted by using the application layer vulnerabilities. That’s why this type of firewall suits mostly the small network system, yet it faces many complexities when applied to larger network systems. Here are the advantages and the disadvantages of this kind of firewall;
Advantages
– The entire traffic of a system can be filtered through a single device.
– Fast and efficient in scanning traffic
– Inexpensive and minimal effect on the other resources.
– End-user experience and fast network performances.
Disadvantages
– Lacks broader context because it works only based on the IP address and port information.
– For not checking the payload of traffic, it can be easily spoofed.
– It could get difficult to set up and manage its access control lists.
– Could trigger complexity while used in a larger network.
2. Stateful Inspection Firewall
Also named dynamic packet filtering, the Stateful inspection firewalls inspect and collect data about the network traffic log and transmit packets through a network system. This type of firewall end to end examines the traffic streams of a computing or network system. Also, these firewalls are known for intelligently handling unauthorized traffic by inspecting the packet headers and the state of the packets. Moreover, it provides proxy services on a system.
The dynamic packet filtering technique works at the network layer of the OSI (Open System Interconnection) model. Compared to the basic filtering system, this type of firewall offers much more robust security with higher consumption of resources at a slower speed. For its performance and security level, it is counted as medium leveled. Here are the advantages and the disadvantages of this kind of firewall;
Advantages
– It monitors IP addresses and payloads as well as the entire session of the state of connection to increase security.
– Provides a high level of control over the contents of data packets of network traffic.
– To allow the incoming or outgoing traffic, it does not require multiple ports.
– It offers substantive logging capabilities.
Disadvantages
– Interferes with the speed, communications, and performance of a network.
– Much resource-intensive, which can affect the performance of a system.
– For the absence of authentication capabilities, it cannot validate the traffic source whether it is spoofed or not.
3. Circuit-level Gateway Firewall
Circuit-level gateway firewalls are designed to protect the private networks from traffic and keep the details private. But, this type of firewall cannot filter the individual data packets passing across the network. Also, it can monitor TCP data packets, which is most important for a private network. This type of firewall consists of the security functions of a system that determines the allowed connection and works at the session layer of the OSI (Open Systems Interconnection) model.
The circuit-level gateway is a stand-alone firewall that can be used to protect anonymity on a private network. Also, this type of firewall can be used in medium-level organizations for inexpensiveness and security levels. Here are the advantages and the disadvantages of this kind of firewall;
Advantages
– It rejects all types of traffic transactions except the requested transactions.
– Easy to set up and manage compared to other types of firewalls.
– Minimum impact on the end-user experience and inexpensive.
Disadvantages
– It does not offer any protection against data leakage unless it is connected with other security functions.
– Doesn’t monitor the application layer of the OSI model.
– This firewall requires ongoing updates to keep the rules updated.
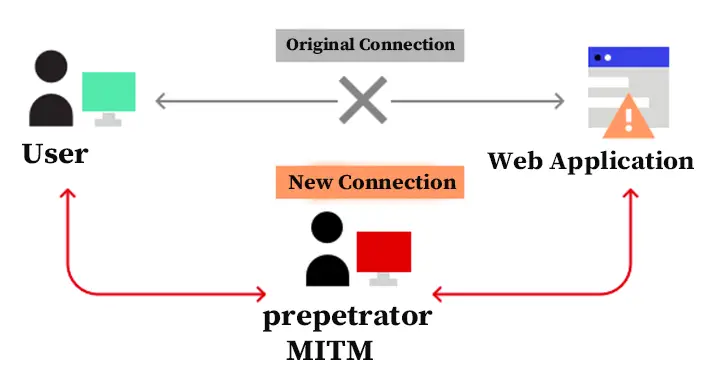
4. Proxy Server/ Application-level Gateway Firewall
Proxy servers or application-level gateway firewalls are the most secure firewall available which uses proxy instead of destination devices to connect. This type of firewall works as a medium to connect the source computer or device with the proxy. Application-level gateway avoids any direct connection or data packet transfer and mirrors the information transfer of either destination of the system. These firewalls are able to mask an IP address and limit the traffic types on a device or network system. Also, these firewalls can effectively protect the system resource by filtering the messages at the application-layer level of the OSI model.
Proxy server firewall provides complete and protocol-aware security on the supported protocols. Through this, it offers the best internet experience and can improve the system’s performance, also it has some limitations that are responsible for affecting its speed, functionality, and overall performance. Despite its limitations, it is the most efficient type of firewall available. Here are the advantages and the disadvantages of this kind of firewall;
Advantages
– Examines all communications including address, information of port and TCP, and the content passing through the proxy of the network.
– Offers well-grounded security control over the traffic.
– Ensures the protection of user anonymity.
Disadvantages
– Expensive and can inhibit network performance.
– To derive the maximum benefit, the application-level gateway requires a high degree of effort.
– It is not suitable for all types of network protocols.
5. Next-gen Firewall
The next-gen or next-generation firewall is the most advanced firewall that offers application-level security on a device and system. Also, this type of firewall also offers fortification against intrusion and intelligence more than any other firewall and this advanced-level firewall ensures all the benefits of a traditional firewall. Moreover, it filters data packets of a system based on the applications. The next-gen firewall can even block or stop the malware from breaching into the network system which is an advanced type of firewall that is able to block evolving and advanced security threats like ransomware and spyware. Despite being the most advanced firewall, the working process of it is most sophisticated compared to other types of firewalls. Here are the advantages and the disadvantages of this kind of firewall;
Advantages
– Combines DPI, malware filtering, and other security controls to ensure the optimum level of filtering of the network traffic.
– It monitors all the traffic of OSI model layers to ensure accuracy.
– The next-gen firewall can be updated to provide updated context.
Disadvantages
– Integrating or combining this type of firewall with other security functions could get complex.
– It is pretty expensive.
Secured Type of Firewall
To choose the most secure type of firewall for a system, you have to find the answer to some firewall-related questions that include protection, resources, expenses, infrastructure, architecture, and other issues. By considering these, you can make the right choice of the firewall to use on your system. Here are the issues that need to consider before choosing the perfect type of firewall for a system;
– Security from threats and protection against malicious programs.
– Monitoring of the contents and traffic inspection process.
– Technical objectives or advantages
– Features and capabilities
– Fitting with the system architecture
The above-described considerations will help you to select and implement the right kind of firewall for your system. All types of firewalls have some advantages and disadvantages, even the most advanced level firewall, the next-gen firewall, has some disadvantages too. So, it is difficult to decide the right type of firewall for a system. In terms of security, the proxy server firewalls are the best choice, while the proxy server firewall is perfect to protect the anonymity of the IP and ports. For advanced level protection, the next-gen firewall is a perfect choice, though it also has some limitations.
The proxy server firewall offers maximum security, and that’s why you need to choose it for your system security. But it has some limitations and impacts while implemented on a system. So, you need to implement incorporate features of different types of firewalls.
Tips: It doesn’t matter whichever type of firewall you decide on for your system, but the configuration of the firewall matters. A misconfigured firewall may give the worst nightmare with your system experience. So, always ensure that the firewall configuration is properly to avoid complications.
Frequently Asked Questions (FAQs)
Is it Possible to Bypass a Firewall?
Though a firewall is secure and protects the operating system from different types of potential threats, a hacker can easily bypass it by utilizing the network or application vulnerabilities. The hackers can bypass the firewall in many ways, the software or application vulnerabilities are mainly responsible for that.
Should I Use a Firewall at Home?
Yes, you need to use a firewall at your home because there is a risk of data leakage or stealing of personal and sensitive data that’s why Setting up a firewall will help you to avoid any type of security threats.
Can a Firewall Prevent Spoofing Attacks?
Well, a firewall can minimize the risk of spoofing attacks on a device or network system. But it cannot entirely stop spoofing attacks. Spoofing attackers are inventing new techniques to spoof, for this reason, the firewall cannot stop the most advanced leveled spoofing attacks, but it can beat most of the spoofing attacks.
Aftermath
At this point, you already know what should be considered to select the most secure type of firewall. The proxy server of a firewall is most secure for small and medium-level organizations when the next-gen firewall is mostly secure for large organizations and that’s all for today, hope you get it, have a great day.