What Is SUNBURST Malware? An Overview
As you know, malicious attacks are increasing day by day. Hackers and cyber attackers are creating new techniques every day to get into a device system. In recent times, the SUNBURST malware attack is an example of that. The techniques of this malware attack were unique for the IT experts. Keep reading this article to know more about the SUNBURST malware attack.
What Is SUNBURST Malware?
Malicious codes can use different techniques to infect a device or to complete the assigned malicious tasks on a device. SUNBURST is a kind of supply chain malicious code that attacks by taking the advantage of the backdoor implementation of the supplier to target and compromise organizations. It is a SolarWinds digitally-signed component of the Orion software framework that was compromised by criminals and hackers. About 33,000 public and private customers had used SolarWinds. The SUNBURST attack was first discovered in December 2019. It was eight months after the original breach; by that time, it had already impacted agencies of some countries including the United States, Canada, Belgium, Britain, and Israel.
What Does SUNBURST Malware Do?
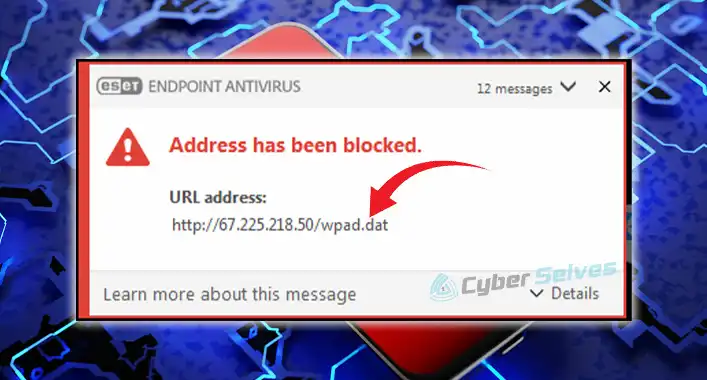
SUNBURST attackers had compromised the SolarWinds software development framework and then used it for building software updates. That allowed the adversaries to patch the update packages as SolarWinds.Orion.Core.Businesslayer.Dll. The framework of this Trojanized SolarWinds contains a backdoor that can communicate using HTTP to the third-party server.
Through the backdoor implementation, this malicious code can execute commands. As you know, it is possible to transfer or execute files, modify the system profiles or system services, and reboot the machine by executing commands. Also, this malicious code is capable to disable the defensive programs running on the targeted system
How to Detect and Remove SUNBURST Malware from the Infected Device?
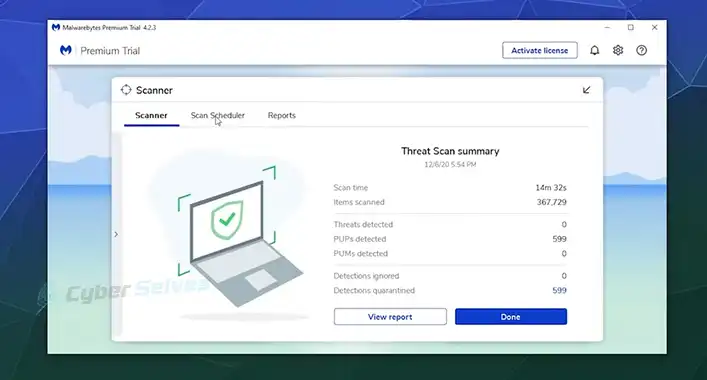
Some security tools can detect and remove SUNBURST from an infected device. Especially the security tools that have the specialized features for analyzing the Trojans. Most modern-day security tools can detect and remove the SUNBURST. A deep scan with an advanced leveled anti-malware program can detect, quarantine, and remove this malicious code from an infected device. Malwarebytes, SpyHunter, and McAfee are some of the security tools that help you kick out the SolarWinds malicious programs from your device.
Frequently Asked Questions (FAQs)
What is Backdoor Malware?
The malicious codes or programs that negate normal authentication procedures to access a system is called backdoor malware. This procedure allows the malware to gain high-level user access to the infected device system.
What Is Supply Chain Attack?
Exploiting trust relationships between an organization and external parties through a malicious attack is called a supply chain attack. This type of malicious attack is mainly conducted to destroy the reputation of a company, organization, or business.
Was SUNBURST Attack a Type of APT?
Yes, the SolarWinds attacks were a kind of advanced persistent threat known as Nobelium. It had started a new wave of supply-chain intrusions using the service provider community.
Finishing Up
After reading the article, you have known enough about the SUNBURST malware attacks. It was a type of APT attack which was conducted by Russian hackers. But, there is nothing to fear now, you can remove it by using an advanced-leveled security tool. That’s all for today, have a great day.