Crypto-Malware Vs Ransomware | The Comparison
Crypto-malware and ransomware are two types of malicious attacks that are performed by hackers to facilitate themselves. Both types of attacks can be the worst nightmare for the user. In this article, we’ll be discussing the comparison between crypto-malware and ransomware. So, let’s start the discussion.

What is Crypto-Malware?
Crypto-malware is a form of malicious code that enables threat actors for Cryptojacking activities. The hackers or cybercriminals use a person’s or organization’s computer system resources to mine cryptocurrency through the crypto-malware without any authorization. This process is called Cryptojacking. A malicious crypto miner program or application is injected into the infected device to mine cryptocurrency. The most common characteristic of crypto-malware is, that it can hide on the device browser and significantly uses the device system resources.
How Does Crypto-Malware Work?
As you already knew, Crypto-malware doesn’t aim for stealing or leaking data or information from a device system. Instead, it utilizes the infected device to continuously and inconspicuously mine for cryptocurrency for as long as possible. It is a silent threat to a device system and disguised as a legitimate program.
That legitimate program embeds malicious code into other programs of the device system after getting in. Whenever the infected device is used, that malicious code runs in the background and mines for cryptocurrency. It uses compromised advertisements or web pages for getting into the device. Upon clicking on these advertisements or visiting these websites, the device gets infected. In most cases, the crypto-malware store itself on the browser, not on-device storage.
What is Ransomware?
Ransomware is a type of malicious code that is deployed by the hackers or malicious actors to hold the user information at ransom through the encryption method. For that, the user losses access to the files, programs, and database of the device system. As you know, the encryption system restricts file access and requires a passkey to open the encrypted files. The attacker demands the ransom from the user against the passkey.
How Does Ransomware Work?
Ransomware uses the asymmetric encryption method, which is a type of cryptography that uses pair of keys to decrypt or encrypt files or programs. That private key is uniquely generated by the attacker for the victim. The attacker only makes the private key available for the user when the ransom is paid. Without the private key, it is nearly impossible to decrypt and access the encrypted files.
In most cases, the ransomware is distributed through email spam or targeted attacks. As you know, the malicious code requires an attack vector for establishing its presence at the endpoint. After that, malware can keep itself hidden on the system until the malicious tasks are completed. Upon getting into a device system, ransomware executes a malicious binary on the system. This malicious binary is responsible for encrypting valuable or important files of the system. Also, it can spread and infect other computers at the same time by using the network system.
After completing the encryption process, it prompts a ransom note for the user, which asks for the ransom to be paid within 24 to 48 hours to decrypt or regain access to the files. Otherwise, the attacker may erase the files or use them to facilitate themselves.
Crypto-Malware Vs Ransomware
Despite being the type of malware, some differences exist between crypto-malware and ransomware. Here we’ll look at the comparisons between these two types of malicious codes below table;
| Crypto-Malware | Ransomware | |
| Definition | Crypto-malware is a form of malicious code that enables threat actors for Cryptojacking activities. The hackers or cybercriminals use a person’s or organization’s computer system resources to mine cryptocurrency through the crypto-malware without any authorization. | Ransomware is a type of malicious code that is deployed by the hackers or malicious actors to hold the user information at ransom through the encryption method. |
| Execution/ Distributing Process | Targeted advertisement or pop-ups, malicious sites, and legit programs. | Spam or malicious email attachments, file transfer system vulnerability. |
| Purpose | Mining cryptocurrency without authorization. | Encrypting the device with a private encryption key. |
| Location of infection | Device browser. | Local storage of the device system. |
| Resource Utilization | Yes. | No. |
| Data Encryption | No. | Yes. |
| Crypto Mining | Yes. | No. |
| Ransom Note | No. | Yes. |
| Stealing Data | No. | Yes. |
| Erasing Data | No. | Yes. |
Frequently Asked Questions (FAQs)
Is Crypto-Malware the Same as a Virus?
Not exactly, crypto-malware and the virus are not the same. Crypto-malware uses the device resource for long-term Cryptojacking while viruses can damage the device or steal important information from a device.
Is It Possible to Decrypt Ransomware Files?
Without the private decryption key, it is nearly impossible to decrypt or access the encrypted files. Because of the asymmetric encryption process, it becomes impossible to decrypt the encrypted ransomware files.
Does Ransomware Steal Data?
In some cases, it is seen that the ransomware-infected data is used by the hackers or attackers to facilitate themselves. But in most cases, it erases the files when the victim failed to pay the ransom.
Conclusion
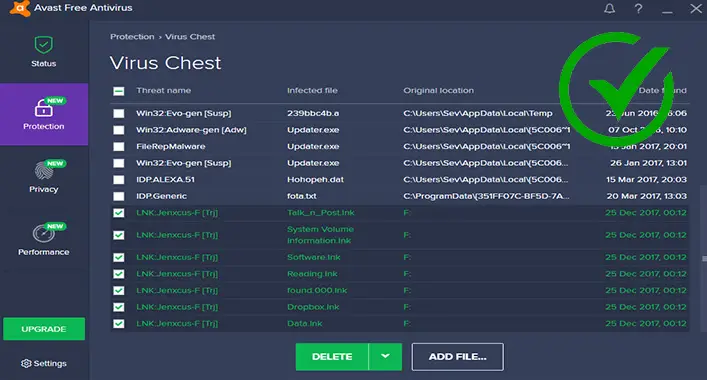
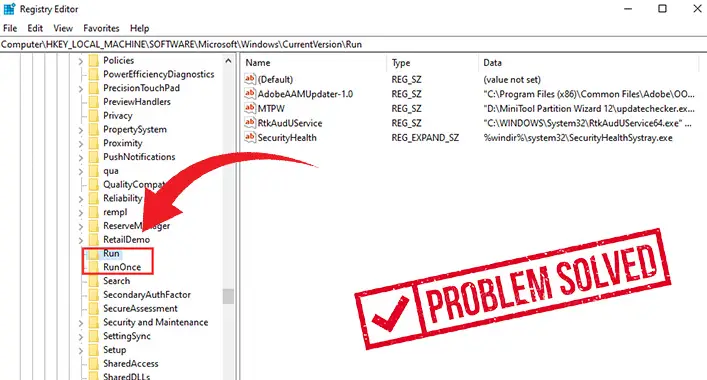
Now, you have known enough about the crypto-malware and ransomware attacks. It is possible to prevent these types of malicious code by using an advanced-leveled anti-malware tool on your device. It is recommended to perform a security check daily to avoid malicious attacks. Well, up to this today, have a great day.
![[Explained] Can a PS3 Get a Virus?](https://cyberselves.org/wp-content/uploads/2023/04/Can-a-PS3-Get-a-Virus.webp)


![[Explained] What Is Avast Emergency Update?](https://cyberselves.org/wp-content/uploads/2022/11/What-Is-Avast-Emergency-Update-768x412.jpg)