How to Respond to a Cyber Attack? A Complete Guide to Do
No matter individual or a business, everyone’s data is vulnerable today. With proper security setup and authentication, still, there are sometimes some data breaches. That is what they do, and they are always on it.

If you experience a cyber attack, there is very little to do at that moment. Once you are attacked, your whole system is compromised. Rather than panicking at that time, go as you have planned before.
But if you don’t know how to respond to a cyber attack, it is time you start to plan ahead. Because this can happen to anyone.
How to Respond to a Cyber Attack on Your Business, Individual Account
Most of the time we start to panic. The milk is out of date? We panic, there’s a storm, and there is no umbrella, panic.
The best way to deal with any situation is to stay calm, try to counter it, and then go forward. That is the only way you can save yourself and your data in the cyber world.
Counter and Prevention
The first and foremost thing to do after a cyber attack is to go against the attack. Most of the time it is malware that has infiltrated your system. Business or personal, you have to disconnect everything and go offline. And then start a thorough scan of your devices and storage. Kill the malware and move on from that point.
Remember, prevention is the key. If you don’t want this to happen again, keep your system secured from every point.
Inform and Communicate
The attacker knows where there is a weak security system. It can be the server or a user’s personal computer. So make sure you inform all your co-worker and the IT department that there is an attack on the server.
This way people will know and take necessary steps from their individual perspectives. Everyone will act like a living organ and it will be easy to pinpoint the entry point of the attack.
And communication is the best way to resolve any issue. Be it a cyber attack or a plan to stop one.
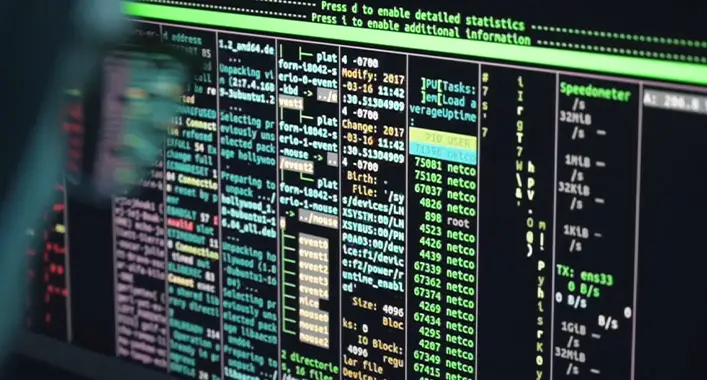
Investigate and Assess Damage
When you have successfully prevented the attack and the malware is removed, it is time to investigate what you have lost, what were they after, and what they have got.
At the same time go through all your security and update any weak points. Salvage anything that you can. And leave the ones that are infected for the tech team to deal with it.
Sometimes you won’t be able to salvage your data as it will cause more damage than doing good. Best you have a backup server with the highest security.
Update and Facilitate System
An attack is as painful and devastating as it can be. Data loss is like losing your money. And sometimes it is about money and assets.
But without an attack, you won’t be able to identify your weak points. When it is all done and everything is put in order, update every little detail you can. Rearrange and facilitate your system.
Without the latest hardware and program, you are as good as having a bug spray in the swamp.
Frequently Asked Questions
How will you respond the cyber attacks?
If you experience a cyber attack, make sure you don’t panic. Because panicking won’t lead to anything good and just waste your time. Rather gather the info of where the attack initiated, what are they after, and what have they got, and counter it with corresponding steps. Talk with your staff and go through your files to eliminate the threat. Then go on investigating what you have lost, what are your weak points, and update your system and security and hardware if needed.
What are the three steps for responding to a cybersecurity threat?
The investigation, assess the damage, and prevention are the three steps for responding to any cybersecurity threat. Missing any one of them may end you up with more attacks
Who responds to cyber threats?
CISA (Cybersecurity and Infrastructure Security Agency) under the supervision of Homeland Security responds to any cyber threats. Any organization or individual under cyber threat should contact them immediately. They have the most advanced tech and team to analyze any threat inside the nation.
What is response in cyber security?
The response in cyber security is the organized step-by-step approach after any cyber attack on your system. It is done so that the threat is identified, neutralized, assessment of the attack, salvaged data, and prevention afterward.
Conclusion
When under an attack of any sort, keeping your calm is the best thing possible. Panicking worsens everything and the attacker will get what they want in the meantime. So keep your calm and go through the steps after any cyber attack and try to eliminate it as soon as possible. Communication is also another key after any attack that reduces the damage by a lot.