How to Prevent Malware Attacks in 2023 | 9 Tips to Protect Your Device from Malware Attacks
Malware attacks are increasing day by day around the world. The hackers or cybercriminals are causing huge damage to the computer resources of a user or organization. But what should you need to do for protecting your computer system against malware attacks? Keep reading this article to know about the measurement should follow to protect your device against malicious attacks on your device.

Why Did My Device Get Hacked?
Hackers or cyber attackers utilize device vulnerabilities to hack or get access to a device. Besides this, they use other hacking techniques to get access to a device. In some cases, they use the browser to get into a secure device. Most IT experts believe that more than 83.6% of hacking and cybercrime is conducted through using device vulnerabilities, browsers, and malicious attachments. The hacker can also use malicious sources and programs to get into a device. Although, some hackers take the advantage of administrative unawareness to get into a device.
How to Prevent Malware Attacks?
To fully protect your device against malware attacks, you need to follow some rules while using the browser and device system for your personal or organizational purposes. By following the below-described steps, you can ensure protection against any type of malware attack;
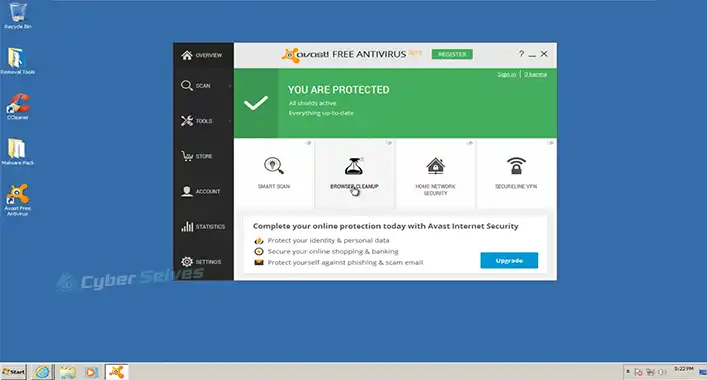
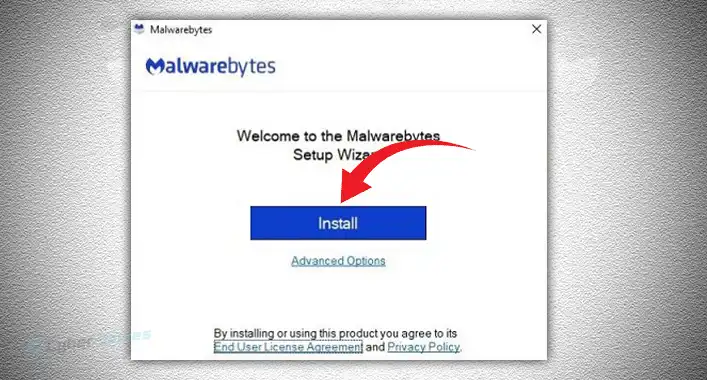
1. Using Security Tools and Firewall
Antivirus or anti-malware tools can scan for malicious existence on a device and remove them. Moreover, these tools can give a device maximum protection against malicious attacks. Some other security tools to monitor the data traffic to detect and take immediate measurements against cyberattacks. Device firewalls do the same thing to protect a device system. So, installing one of the most advanced types of security tools and keeping the updated version of the firewall will be a major step against malicious attacks.
2. Safe Browsing
While browsing, avoid unsecured sites and never download any attachments from any unsecured websites. Because the unsecured websites can deliver or inject malicious code to your device through an attachment. So, you need to be aware while surfing the internet. Also, some browser attachments (Extensions/Add-on) can facilitate the attackers to conduct malicious attacks.
3. Multi-Factor Authentication Method
The multifactor authentication method ensures the security of login credentials against any type of malicious attack. Most modern-day services have multifactor authentication features to kick out the security concern of a user. So, enabling it will safeguard your login credentials even if you are a victim of malicious attacks.
4. Updated Version of Programs and Drivers
The updated version of the program and drivers are less vulnerable to malicious attacks compared to the older version. As you know, an update of a program or driver can fix the bugs and glitches that can be used to conduct malware attacks on your device. Keeping the updated version of the program and driver can beat the malicious attackers.
5. Controlling System Access
Stopping the data from breaching the system through regulating networks is essential for controlling access to a system. You can follow multiple tips to regulate the network system;
– Installing a firewall on the system.
– Implementing IDS (Intrusion Detection System) and IPS (Intrusion Prevention System).
– Avoid unfamiliar remote drives or media.
– Disable unused ports and protocols.
– Removing inactive user accounts from the system.
– Check the licensing agreements and certificates before installing programs on the system.
6. Limiting Application Privileges
Restricting the application privileges will limit the number of possible entryways for malware attacks. It is better to allow only the application features and functions that are necessary to run the application properly on the device system.
7. Monitoring Activities or Process
Some malware attacks can last long by hiding the malware/malicious codes in the core system files of the operating system. These are the deadliest malware attacks, which only can be detected through monitoring data traffic and reviewing the running process. Also, it enables the admin to inspect all types of data traffic on a system.
8. Using Trusted Sources
Always using trusted sources to transfer files will keep a device secure against malicious attacks. Use a trusted source to download programs or files to download and scanning the email attachments before opening them will make your device secure against malware attacks.
9. Encryption and VPN
End-to-end encryption and VPN (Virtual Private Network) keep your data and data packets private. If you use encryption and VPN, it is nearly impossible to access your data even when your device is infected.
Frequently Asked Questions (FAQs)
What Does a Phishing Link Look Like?
The phishing links look more peculiar than the usual website links. As you know, any data passed on a website is insecure and could be intercepted by hackers or third parties, except HTTPS or HTTP. Phishing sites never use HTTPS or HTTP protocols. By reviewing the URL address, you can easily identify a secure or insecure web link.
How Do You Know If a Site Is Suspicious?
To know whether a site is suspicious or not, you need to check the URL address. If you find HTTPS or SHTTP on the address; it is a secure link. Otherwise, the link is suspicious.
What Is Typosquatting?
Typosquatting or URL hijacking is a social engineering malware attack that uses misspelled domains to conduct the attack. These misspelled URL uses the copyright and legitimacy of other domain.
Aftermath
At this point, you have known enough about how to prevent malware attacks. Hope, these measurements will be enough to keep your device secure against the most advanced malicious attacks. Remember to use security tools to keep the device system secure. That’s all for today, have a great day.